VA EA Security Domain
 Protecting our critical infrastructure, assets, networks, systems, and data is one of the most significant challenges our country faces in today’s Internet-based IT environment. Every day, our Nation experiences increasingly sophisticated cyber threats and malicious intrusions. Not surprisingly, in 1997 GAO designated Federal information security as a government-wide high-risk area (see GAO Report on Federal Information Security: Agencies Need to Correct Weaknesses and Fully Implement Security Programs).
Protecting our critical infrastructure, assets, networks, systems, and data is one of the most significant challenges our country faces in today’s Internet-based IT environment. Every day, our Nation experiences increasingly sophisticated cyber threats and malicious intrusions. Not surprisingly, in 1997 GAO designated Federal information security as a government-wide high-risk area (see GAO Report on Federal Information Security: Agencies Need to Correct Weaknesses and Fully Implement Security Programs).
Domain Scope
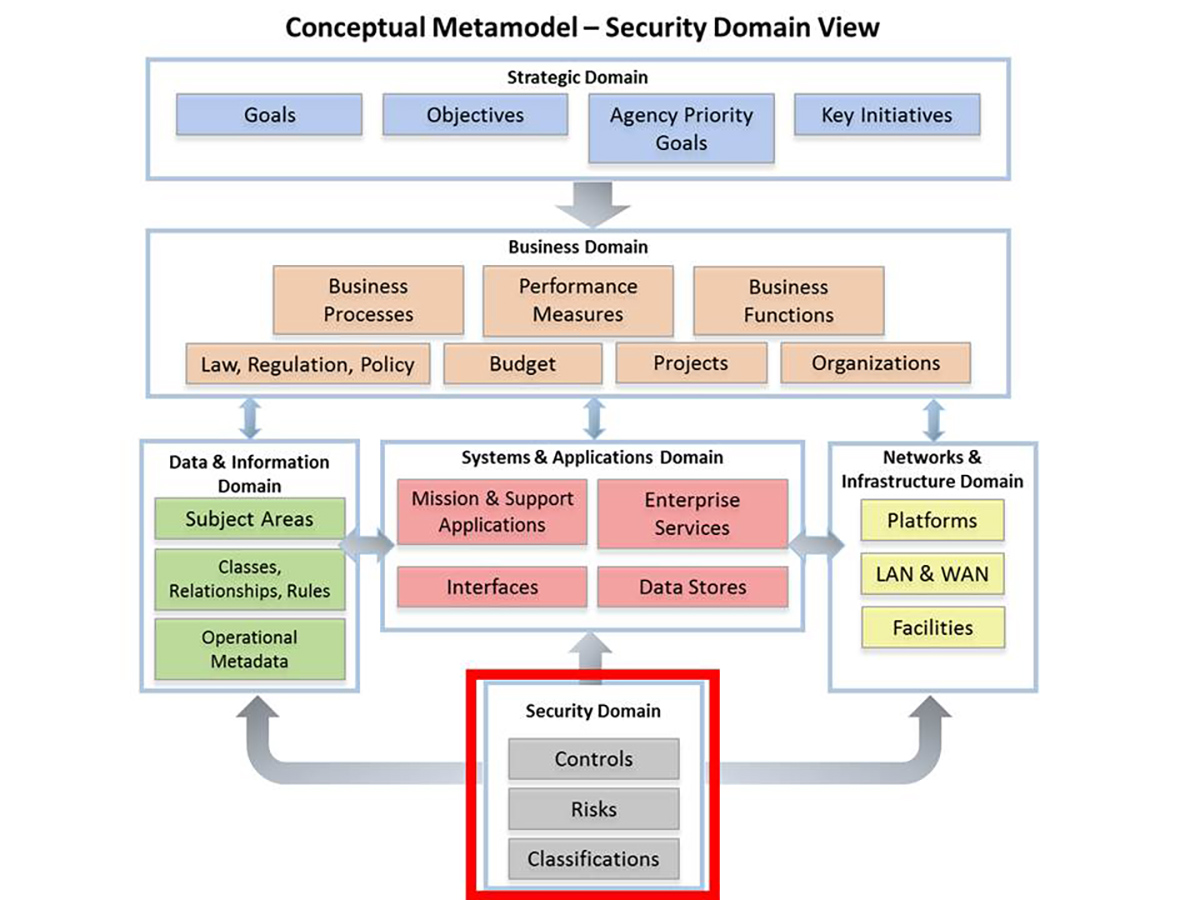
The Security Domain describes what VA must do to protect sensitive personal customer and employee information and ensure its cyberspace ecosystem is secure, ready, resistant, and resilient from threats, unauthorized access, and vulnerabilities. According to the Conceptual Metamodel below, the scope of this Domain includes security-related strategies, plans, laws, policies, regulations, capabilities, standards, practices, and performance measures.
Conceptual Metamodel – Security Domain View
Relationships
The Security Domain information is closely linked to all other domains because security is integral to the overall security posture and health of an organization and/or system. These linkages:
- Describe the relationships between the Department’s cybersecurity strategy, goals, and objectives and enabling capabilities, functions, business processes, information, infrastructure, and technology needs
- Identify the laws, policies and regulations, and technical standards that must be met to ensure a compliant and secure IT operating environment
- Identify enterprise services that deliver security-related functions at lower cost than new development
- Provide standards related to sharing of information among systems, lines of business, customers, and partner providers
- Enable the establishment of a common “language” for information security within the Department
When this Metamodel and its relationships are fully developed, the information captured in this Domain can be used to enable the adoption of the latest technology innovations and help identify candidate systems, applications, and platforms for remediation or retirement due to security risks. By successfully addressing the cybersecurity risk in VA’s technology environment, VA will be able to provide trusted access and sharing of information within the ecosystem of Veteran service providers, thus ensuring confidence in VA.
Future Enhancements
As the Enterprise Cybersecurity Strategy continues to mature and evolve, the VA EA will be updated. This will include the addition and integration of all relevant security requirements to support critical aspects of the strategy that must be followed and enforced within VA business processes during the development, implementation, and execution of IT solutions.
Key EA Artifacts Currently Available
Strategic Guidance
- Enterprise Cybersecurity Strategy and Enterprise Cybersecurity Strategy Fact Sheet – focuses on building a comprehensive cybersecurity capability that spans VA and the cyberspace ecosystem in which VA personnel, its customers, and its partners operate.
White Papers/Tech Insights
- List of security related documents are available at the Tech Insights page.
Models, Patterns, and Reports
- List of Enterprise Design Pattern documents are available at the Enterprise Design Patterns page.
VA Policies, Guidance, and Statutes
- VA Directive 6500 – Information Security Program (20 Sep 2012)
- VA Handbook 6500 – Risk Management Framework for VA Information Systems – Tier 3: VA Information Security Program (10 March 2015)
- VA Directive 6517 – Risk Management Framework for Cloud Computing (15 Nov 2016)